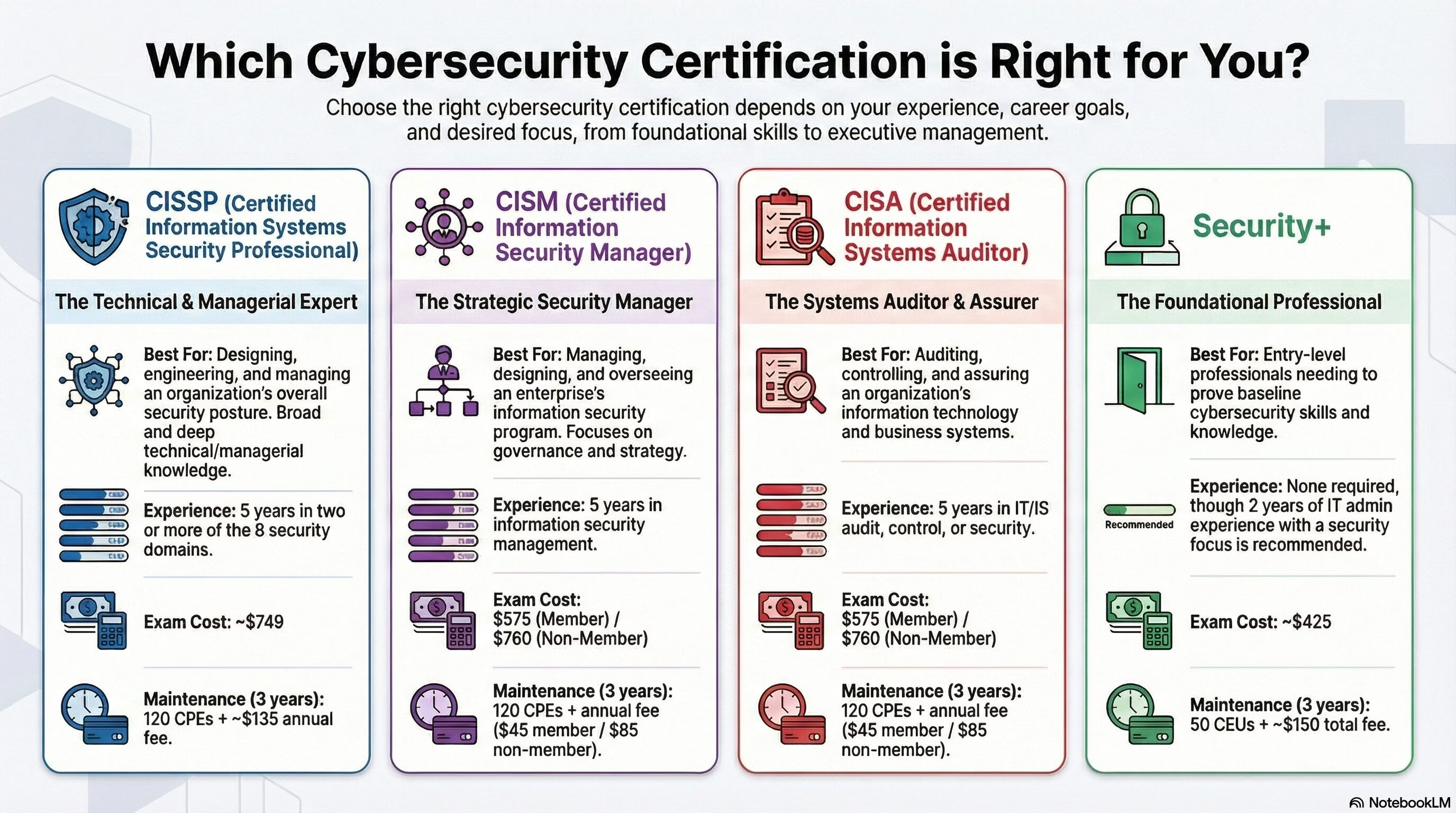
Here is a detailed comparison of the four major cybersecurity certifications—CISSP, CISM, CISA, and Security+—designed to help you decide which path fits your career goals. Quick Comparison Table Feature Security+ (CompTIA) CISSP (ISC2) CISM (ISACA) CISA (ISACA) Best For… Beginners… Read More "Which certification to choose: CISSP, CISM, CISA or Security+?"